





Windows Recall Security Breach Exposes E-Commerce Seller Data Risk | Critical AI Privacy Vulnerability
- Microsoft's AI screenshot feature compromised by TotalRecall Reloaded exploit; sellers using Windows 11 face exposure of customer data, payment info, and business communications captured in Recall vault









Overview
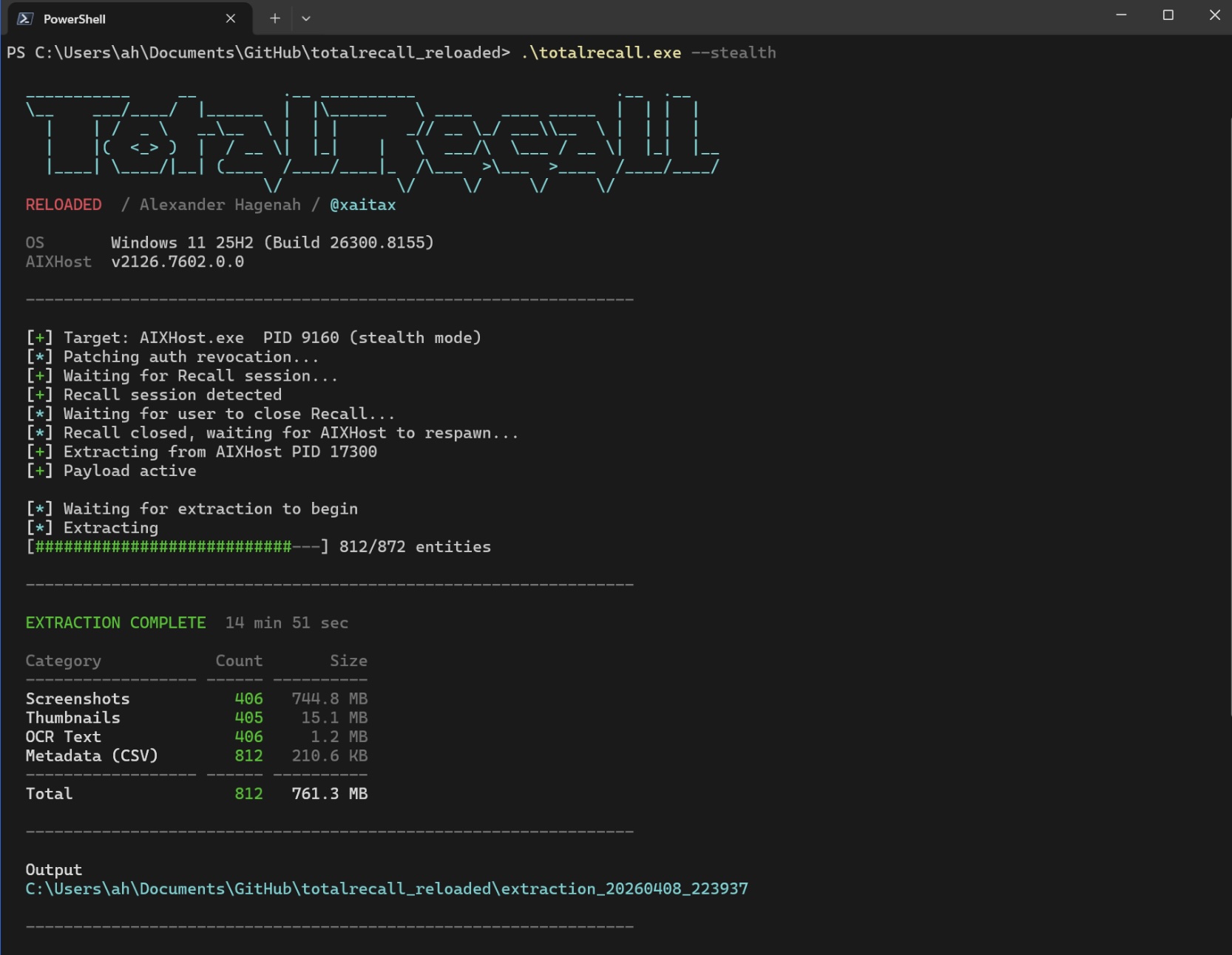
Windows Recall's critical security vulnerability, disclosed by researcher Alexander Hagenah in March 2025, creates immediate data protection risks for e-commerce sellers relying on Windows 11 systems. The TotalRecall Reloaded exploit bypasses Microsoft's encryption and VBS Enclave protections by intercepting decrypted content sent to unprotected rendering processes, allowing attackers to extract the entire Recall vault containing browsing history, emails, private messages, and all on-screen text. For e-commerce sellers, this represents a catastrophic exposure vector: customer payment information, supplier communications, inventory management systems, Amazon Seller Central credentials, Shopify admin access, and confidential business data captured in screenshots are now vulnerable to extraction by dormant malware.
The architectural flaw undermines Microsoft's security model fundamentally. While the company implemented strong cryptographic protections and biometric authentication (Windows Hello), the vulnerability exists in how decrypted content flows to unprotected processes—creating what Hagenah describes as "titanium vault doors with drywall walls." Microsoft's controversial response, claiming the access patterns are "consistent with intended protections," provides no reassurance for sellers managing sensitive business operations. The company's acknowledgment of timeout and anti-hammering protections offers minimal mitigation when attackers can remain dormant in background processes and extract entire vault contents during legitimate user authentication sessions.
For e-commerce sellers, the operational impact is severe and immediate. Sellers using Windows 11 with Recall enabled face exposure of: (1) Customer PII and payment card data captured during order processing, (2) Supplier communications and pricing negotiations visible in email screenshots, (3) Inventory management system credentials and stock data, (4) Marketplace account credentials for Amazon, eBay, Shopify, and other platforms, (5) Financial records and tax documentation visible during accounting software use. A comprehensive fix requires fundamental OS redesign—not a simple patch—meaning this vulnerability will persist for months or years. Sellers cannot rely on Microsoft's timeline for resolution, making immediate mitigation essential. The incident highlights the tension between AI feature functionality and security implementation in Windows, with sellers bearing the risk of Microsoft's architectural compromises.
**Immediate seller actions: (1) Disable Windows Recall immediately in Settings > Privacy & Security > Activity History, (2) Audit which business systems and credentials were used on affected Windows 11 machines, (3) Reset passwords for Amazon Seller Central, Shopify, eBay, and payment processor accounts accessed on vulnerable systems, (4) Review Recall timeline history (if accessible) to identify what sensitive data was captured, (5) Consider isolating Windows 11 systems from business-critical operations until Microsoft releases a comprehensive security patch. Strategic adjustments: Evaluate shifting sensitive business operations to non-Windows systems or air-gapped machines for credential management and financial operations. Monitor Microsoft's security updates closely—a fundamental OS redesign may take 6-12 months. Risk mitigation: Document all systems with Recall enabled, implement hardware security keys for marketplace account access, and consider cyber liability insurance covering data breach scenarios from OS vulnerabilities.