




Critical Windows Security Threats Impact E-Commerce Infrastructure | April 2026
- Three unpatched zero-days (BlueHammer, RedSun, UnDefend) actively exploited since April 10, 2026; sellers operating Windows-based inventory and payment systems face elevated data breach risk



%20(1).webp)









Overview
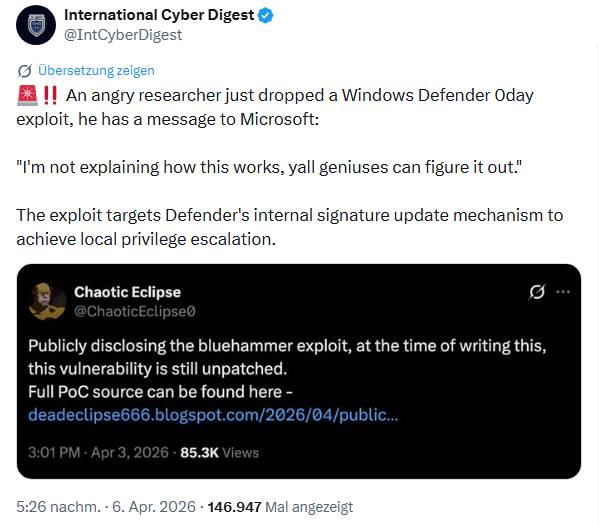
Critical Windows vulnerabilities disclosed in April 2026 pose direct operational risks to e-commerce sellers managing inventory, accounting, and payment processing on Windows infrastructure. Three zero-day exploits—BlueHammer (CVE-2026-33825), RedSun, and UnDefend—have been actively weaponized since April 10, 2026, according to Huntress Labs security researchers confirming "hands-on-keyboard threat actor activity" on compromised Windows devices. While Microsoft patched BlueHammer in April 2026 security updates, RedSun and UnDefend remain unpatched across Windows 10, Windows 11, and Windows Server 2019+ systems, creating a critical vulnerability window for sellers relying on Windows-based infrastructure.
For e-commerce sellers, the operational impact is substantial and multi-layered. Sellers operating Windows servers for inventory management systems (IMS), accounting software (QuickBooks, Xero), or payment processing face elevated risk of system compromise, data theft, and operational downtime. The RedSun exploit specifically abuses Windows Defender's cloud tagging behavior, allowing attackers to overwrite critical system files and escalate privileges to SYSTEM level—the highest privilege tier in Windows. This means attackers gaining initial access to a seller's Windows infrastructure can rapidly achieve administrative control, access customer payment data, modify inventory records, and move laterally across networks. For sellers managing 1,000+ SKUs or processing $50K+ monthly revenue through Windows-based systems, a single compromise could result in $10K-50K+ in recovery costs, customer notification expenses, and potential platform suspension if customer data is breached.
The vulnerability disclosure context reveals systemic risks beyond the technical flaws. Security researcher "Nightmare-Eclipse" released RedSun publicly on April 16, 2026, following frustration with Microsoft's Security Response Center (MSRC) vulnerability disclosure process, with explicit threats of releasing additional remote code execution (RCE) exploits. This researcher-versus-vendor tension means exploit code is now freely available on GitHub, dramatically lowering the barrier for threat actors to weaponize these vulnerabilities. Sellers cannot rely on patch timelines—Microsoft has not announced patch dates for RedSun or UnDefend—making immediate mitigation essential. The unpatched status means all current Windows 10 and 11 installations remain vulnerable, affecting an estimated 1.4 billion Windows devices globally, including thousands of e-commerce seller operations.
Immediate seller impact varies by infrastructure architecture. Sellers using cloud-based platforms (Amazon Seller Central, Shopify, eBay) with minimal Windows server dependency face lower risk. However, sellers operating dedicated Windows servers for inventory synchronization, accounting integration, or payment gateway processing face critical exposure. The exploit's reliance on Cloud File API and Windows Defender behavior suggests systems with cloud synchronization enabled (OneDrive, Google Drive, Dropbox integration) are particularly vulnerable. Sellers managing multi-channel operations across Amazon, eBay, and Shopify using Windows-based inventory sync tools are at elevated risk of data exfiltration affecting all sales channels simultaneously.