



Windows Server Patch Crisis Threatens E-Commerce Infrastructure | KB5082063 Stability Issues
- April 2024 patches KB5082063, KB5083769, KB5082052 create domain controller failures, BitLocker lockouts affecting thousands of enterprise sellers managing inventory, payment, and logistics systems on Windows Server 2016-2025





%20(1).webp)











Overview
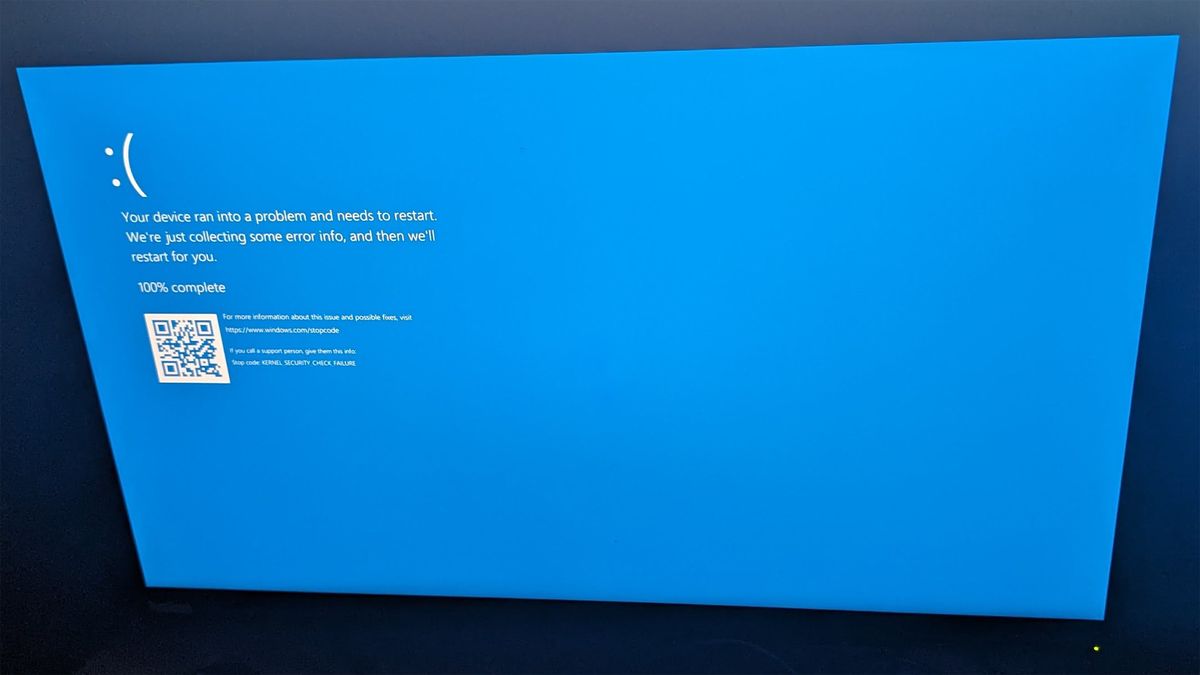
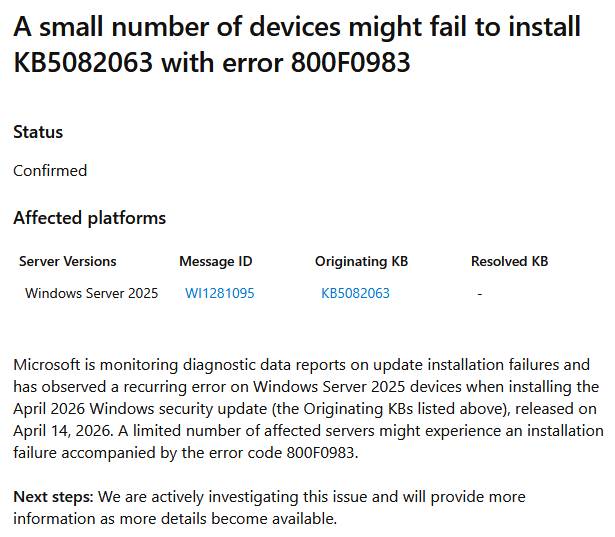
Microsoft's April 2024 Patch Tuesday updates have created a cascading infrastructure crisis affecting e-commerce sellers relying on Windows Server infrastructure for critical business operations. The cumulative update KB5082063, released to address the rogue Windows Server 2025 upgrade incident that began in 2024, has introduced at least three documented critical issues: domain controller reboot loops affecting Windows Server 2016, 2019, 2022, and 2025; BitLocker recovery key prompts on Windows 11 enterprise systems (KB5083769, KB5082052); and LSASS crashes in Privileged Access Management (PAM) environments. For cross-border e-commerce sellers operating enterprise infrastructure, these patches directly threaten operational continuity of inventory management systems, payment processing platforms, and logistics software that depend on stable Windows Server domain controllers for authentication and directory services.
The domain controller reboot loop issue represents the most severe threat to seller operations. When affected domain controllers enter continuous restart cycles, they prevent network authentication, user login, and directory services from functioning—effectively rendering entire business domains unavailable. This creates immediate operational risks for mid-market and enterprise sellers managing 1000+ SKUs across multiple fulfillment channels. The incident marks the third documented problem from KB5082063, indicating quality assurance gaps in Microsoft's testing procedures. Organizations running Windows Server infrastructure have faced a critical choice: deploy security patches and risk infrastructure instability, or delay patching and accept security vulnerabilities. Microsoft committed to releasing corrective fixes "within days," but the extended timeline from initial Windows Server 2025 upgrade incident (emerged 2024, officially closed 2025) demonstrates the complexity of addressing widespread infrastructure issues affecting thousands of organizations globally.
BitLocker encryption conflicts add secondary operational disruption for Windows 11 enterprise workstations. The April updates trigger unexpected BitLocker recovery key prompts on systems with specific configurations (TPM validation profiles, PCR7 binding, UEFI firmware), requiring IT intervention to resolve. While recovery occurs only once per affected system, organizations managing thousands of enterprise workstations face widespread support ticket volume and user confusion. Microsoft provides fast-track preventive solutions through Group Policy configuration adjustments (TPM validation policy set to Not Configured, followed by BitLocker suspension/re-enablement) or Known Issue Rollback (KIR) deployment. For sellers managing distributed teams across multiple locations, these workarounds require coordinated IT deployment across potentially hundreds of workstations, consuming IT resources during critical business periods. The incident underscores the operational risk of aggressive patch deployment schedules in environments where system stability directly impacts revenue-generating operations like order processing, inventory management, and customer service platforms.