





Critical Microsoft Security Vulnerabilities Threaten E-Commerce Operations | Patch Deadline April 28
- Over 1,300 SharePoint servers and legacy Excel systems actively exploited; federal agencies face 2-week compliance deadline affecting government contractors and cross-border sellers







Overview
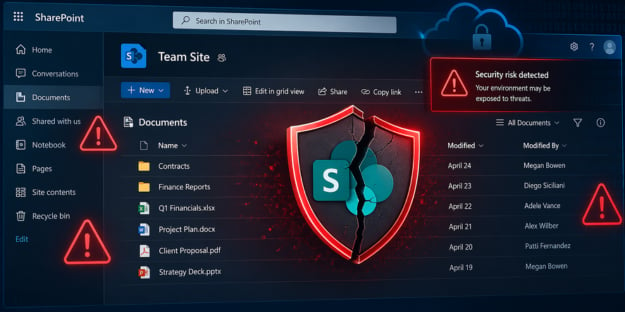
Critical security vulnerabilities in Microsoft SharePoint and Excel pose immediate operational risks to cross-border e-commerce sellers managing inventory, financial records, and supplier communications. Between April 14-26, 2026, Microsoft released patches for CVE-2026-32201 (SharePoint spoofing vulnerability affecting 1,370+ IP addresses globally) and CVE-2009-0238 (18-year-old Excel remote code execution flaw). The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added both vulnerabilities to its Known Exploited Vulnerabilities catalog, mandating federal agencies patch systems by April 28, 2026—a deadline that cascades to government contractors and regulated e-commerce businesses.
SharePoint vulnerability impacts inventory and supply chain operations. The CVE-2026-32201 flaw affects SharePoint Enterprise Server 2016, 2019, and Subscription Edition through improper input validation, enabling unauthenticated network spoofing attacks. ShadowServer reported fewer than 200 of 1,300+ vulnerable systems patched as of late April 2026, indicating widespread exposure. For e-commerce sellers using SharePoint for inventory management, supplier communications, and document collaboration, successful exploitation allows unauthorized data access and modification—directly threatening business continuity. The vulnerability impacts confidentiality and integrity, exposing sensitive product catalogs, pricing data, and supplier contracts to threat actors.
Legacy Excel systems create supply chain attack vectors. CVE-2009-0238, despite being 18 years old, remains actively exploited against unpatched systems. The vulnerability enables remote code execution when users open malicious Excel files, allowing complete system hijacking. E-commerce sellers managing inventory spreadsheets, financial records, and customer data on outdated Excel versions face data breaches and operational disruption. The threat extends to supply chain partners—vendors sending Excel files containing malicious payloads can compromise entire seller networks. CISA's inclusion of this ancient vulnerability in actively exploited lists signals ongoing real-world attacks against organizations with inadequate patch management.
Regulatory compliance creates operational urgency. The April 28 federal deadline applies directly to government agencies and contractors, but extends to regulated e-commerce businesses operating in compliance-heavy sectors (financial services, healthcare, government procurement). Sellers unable to patch must discontinue SharePoint/Excel use or implement vendor-recommended mitigations, disrupting normal business operations. The slow patching rate (85% of SharePoint systems remain unpatched) suggests many organizations lack robust patch management protocols, creating systemic risk across supply chains.