





AI-Powered Vulnerability Discovery Reshapes E-Commerce Security Compliance | 2,000+ Zero-Days Demand Urgent Data Protection Overhaul
- Anthropic's Mythos AI discovers 2,000 vulnerabilities in 7 weeks (30% of annual zero-day output); forces e-commerce platforms to shift from perimeter defense to data-centric security architecture within 90-180 days

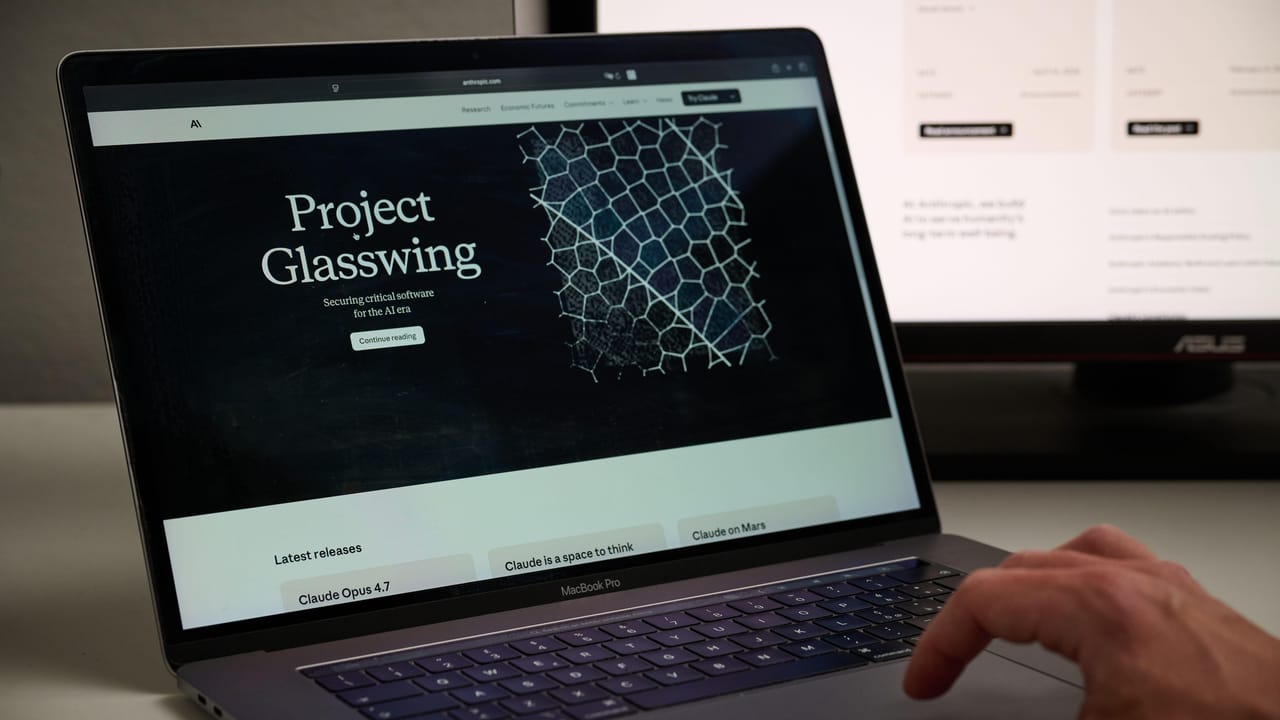









Overview
Anthropic's Mythos AI has fundamentally disrupted cybersecurity vulnerability discovery, uncovering 2,000 previously unknown software vulnerabilities in just seven weeks of testing—equivalent to 30% of the world's entire annual zero-day vulnerability output. This breakthrough represents a critical inflection point for e-commerce compliance, as the technology dramatically lowers the barrier to exploitation. Individuals without specialized cybersecurity training can now identify and exploit serious software flaws, a capability previously requiring substantial expertise. For e-commerce sellers and platforms, this development triggers immediate regulatory and operational pressure.
The compliance implications are severe and multi-layered. Traditional perimeter defense strategies—firewalls, network monitoring, endpoint security—have consumed hundreds of billions in investment but cannot keep pace with AI-accelerated threat discovery. The attack lifecycle has compressed from weeks to hours or minutes, rendering manual security architectures obsolete. E-commerce platforms storing customer banking information, medical records, and retail account data face exponentially increased breach risk. Regulatory bodies (GDPR, CCPA, PCI-DSS) are already signaling that legacy security models no longer satisfy compliance standards. Sellers must anticipate that platforms will mandate data-centric security implementations—object-level protection, real-time access controls, and continuous audit capabilities—within 90-180 days. Non-compliance will result in account suspension, data breach liability, and potential regulatory fines ranging from $10,000-$50,000+ per incident.
The strategic shift from perimeter to data-centric security creates both compliance barriers and competitive opportunities. Platforms with restricted access to Mythos (Microsoft, Google, trusted partners) gain defensive advantages, while non-integrated sellers face asymmetric pressure: attackers need succeed only once, while defenders must succeed continuously. This dynamic will accelerate consolidation toward mega-platforms offering integrated security infrastructure. Sellers must immediately audit their data handling practices, implement encryption at rest and in transit, establish role-based access controls, and deploy real-time monitoring. Third-party compliance service providers offering data governance, vulnerability scanning, and incident response will experience 40-60% demand surge. Categories handling sensitive customer data (financial services, health products, luxury goods) face the highest compliance costs ($5,000-$25,000 annually for mid-sized sellers) but gain competitive moats against non-compliant competitors. The window for voluntary compliance adoption is 60-90 days before regulatory enforcement intensifies.