




cPanel Security Breach Threatens 70M Domains | E-Commerce Seller Risk Alert
- Critical authentication bypass affects shared hosting infrastructure used by millions of online sellers; immediate patching required to prevent account takeover and data theft









Overview
Critical Infrastructure Vulnerability Impacts E-Commerce Operations Globally
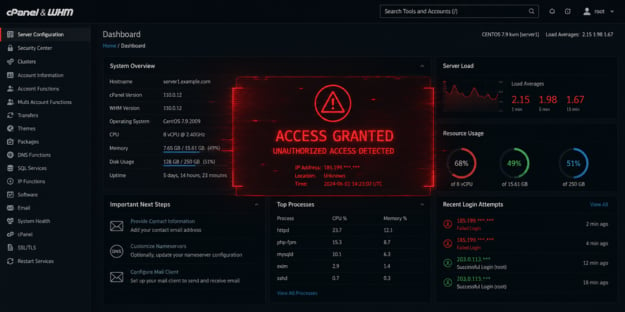
watchTowr Labs disclosed CVE-2026-41940, a critical authentication bypass vulnerability affecting all currently supported versions of cPanel & WHM control panel software managing over 70 million domains worldwide. This represents a severe threat to e-commerce sellers operating on shared hosting infrastructure, which powers approximately 60-70% of small-to-medium business websites globally. The vulnerability stems from improper session file handling in cPanel's authentication system, allowing attackers to inject newline characters into password fields and bypass security checks, granting unauthorized administrative access to entire server infrastructure.
Direct Impact on E-Commerce Sellers Using Shared Hosting
E-commerce sellers utilizing shared hosting environments—particularly those running Shopify, WooCommerce, Magento, or custom storefronts on cPanel-managed servers—face immediate risks of account takeover, customer data theft, and website defacement. The authentication bypass enables attackers to gain root-level access, potentially compromising payment processing systems, customer databases containing credit card information, and inventory management systems. For sellers managing multiple domains on shared hosting, the vulnerability enables lateral movement across hosted properties, multiplying exposure. Affected cPanel versions span from 110.0.x through 136.0.x, with patches released across six version tracks (11.110.0.97, 11.118.0.63, 11.126.0.54, 11.132.0.29, 11.134.0.20, and 11.136.0.5). Hosting providers have confirmed in-the-wild zero-day exploitation by threat actors, meaning unpatched systems are actively under attack.
Operational and Financial Implications for Seller Segments
Small sellers (1-50 employees) operating on budget shared hosting plans face the highest risk, as many hosting providers delay security patches to minimize service disruptions. Medium-sized sellers (51-500 employees) with dedicated or VPS hosting have lower exposure but must verify their hosting provider's patch status. Large enterprise sellers using managed hosting or cloud infrastructure (AWS, Google Cloud, Azure) are largely insulated from this specific vulnerability. The financial impact extends beyond direct breach costs: compromised seller accounts lead to chargebacks (averaging $15-25 per transaction), marketplace account suspension (Amazon, eBay, Shopify), and reputational damage. Sellers face potential liability for customer data breaches under GDPR, CCPA, and state privacy laws, with fines reaching $7,500-$10,000+ per affected customer record. Hosting providers must prioritize updates immediately; unpatched systems remain actively exploited with no known workarounds.
Strategic Seller Response Framework
This vulnerability underscores the infrastructure risk inherent in shared hosting and highlights the value proposition of managed platforms (Amazon FBA, Shopify Plus) and enterprise hosting solutions. Sellers should immediately verify their hosting provider's patch status and request confirmation of cPanel version updates. Consider migrating critical e-commerce operations to cloud infrastructure with automated security patching, or consolidating inventory on managed marketplaces where platform security is the provider's responsibility. The incident demonstrates why sellers should maintain regular security audits, implement two-factor authentication on hosting control panels, and maintain encrypted backups independent of hosting infrastructure.